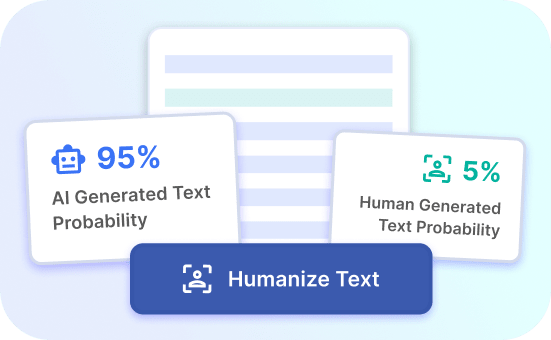
AI Detection Bypassed
Discover how Justdone.ai can help you bypass AI detection effortlessly and effectively for your needs.
Justdone.ai Benefits
Enhanced AI Evasion
Justdone.ai offers enhanced capabilities to bypass AI detection effectively and effortlessly, ensuring your content reaches its intended audience.
Seamless Detection Evasion
With Justdone.ai, experience seamless AI detection evasion, allowing you to focus on your content without worrying about restrictions.
Effortless Bypassing Solution
Justdone.ai provides an effortless solution for bypassing AI detection, ensuring your content remains visible and accessible to your target audience.
Bypassing AI Detection: Benefits You Can't Ignore
Enhanced Security
Bypassing AI detection enhances security by preventing unauthorized access to sensitive information. By using advanced techniques to bypass AI detection, businesses can safeguard their data from malicious cyber threats and potential breaches. This ensures that valuable data remains protected and confidential.
Furthermore, enhanced security measures instill trust and confidence among customers, reassuring them that their personal information is secure. This can lead to improved customer satisfaction and loyalty, ultimately benefiting the business's reputation and credibility.
Try Justdone ->
Uninterrupted Operations
By bypassing AI detection, businesses can ensure uninterrupted operations without being hindered by restrictive algorithms. This allows for seamless functionality and performance, enabling organizations to maintain productivity and efficiency. Uninterrupted operations contribute to consistent service delivery and customer satisfaction.
Moreover, bypassing AI detection can prevent false positives or erroneous restrictions that may impede legitimate user activities. This promotes smooth and uninterrupted user experiences, fostering positive interactions and sustained engagement.
Try Justdone ->
Strategic Advantage
Gaining the ability to bypass AI detection provides a strategic advantage in competitive landscapes. It empowers businesses to adapt to evolving technologies and stay ahead of potential limitations posed by AI algorithms. This agility allows for innovation and flexibility in implementing tailored solutions.
Additionally, bypassing AI detection can enable organizations to explore new opportunities and markets that may have been restricted by conventional AI parameters. This strategic advantage opens doors to untapped potential and empowers businesses to pursue growth and expansion.
Try Justdone ->
Effective Strategies for Bypassing AI Detection
Anonymity Preservation
Maintain anonymity by incorporating encryption and obfuscation techniques to conceal sensitive data and user identities. Utilize secure communication channels and authentication methods to prevent AI detection of identifiable information. This ensures privacy protection and shields against tracking and monitoring.
Behavioral Adaptation
Implement adaptive behavioral patterns that mimic natural human interactions to evade AI detection. Vary user actions and access frequencies to avoid predictable patterns. By simulating authentic behaviors, businesses can bypass AI algorithms and mitigate the risk of detection and restriction.
Dynamic Evasion Tactics
Employ dynamic evasion tactics such as pattern randomization and algorithmic camouflage to evade AI detection mechanisms. Continuously adapt evasion strategies to counter evolving detection methods and enhance resilience against detection algorithms. Dynamic tactics bolster defense mechanisms and deter AI identification.
Contextual Disguise
Utilize contextual disguise techniques to modify data attributes and contextual information, making it ambiguous to AI detection systems. By obscuring contextual cues and altering data representations, businesses can bypass AI scrutiny and operate within the desired parameters. Contextual disguise enhances stealth and deception against detection mechanisms.
Adversarial Training
Engage in adversarial training to fortify AI evasion capabilities through iterative learning and adaptation. Develop countermeasures to adversarial attacks and refine evasion strategies to outmaneuver AI detection. Adversarial training enhances resilience and prepares businesses to navigate evolving AI landscapes effectively.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
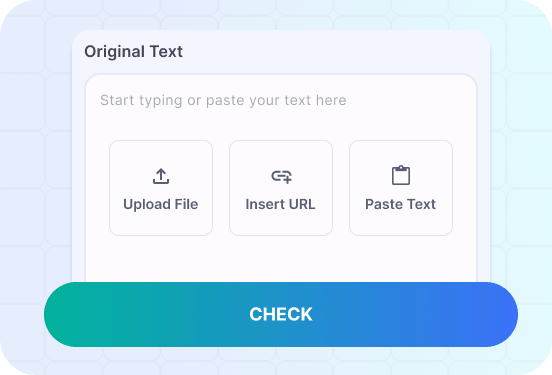
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Exploring Effective Bypassing AI Detection Techniques
Discover the practical application of bypassing AI detection through real-world scenarios and solutions. Gain insights into effective tactics and strategies for evading AI algorithms and maximizing operational potential.
Craft a scenario where a user's behavior adapts to evade AI detection while accessing sensitive information. Emphasize the seamless integration of adaptive tactics and the successful bypassing of AI algorithms.
In a bustling corporate environment, an employee seeks to access confidential project details and sensitive financial reports. Aware of stringent AI monitoring, the user strategically varies access timings and alters interaction patterns to simulate natural browsing behaviors. By incorporating sporadic access intervals and diverse browsing sequences, the user effectively evades AI detection, ensuring unhindered access to vital information.
The adaptive tactics employed mirror authentic user behaviors, circumventing AI algorithms and bypassing detection mechanisms. This seamless integration of adaptive strategies enables the user to navigate through AI scrutiny undetected, preserving operational fluidity and data accessibility. The successful evasion of AI detection underscores the efficacy of behavioral adaptation in safeguarding sensitive information and maintaining operational integrity.
Furthermore, the user's adept utilization of adaptive tactics reinforces the significance of dynamic evasion strategies in countering AI surveillance. By strategically adapting behaviors to outmaneuver detection mechanisms, the user exemplifies the practical application and effectiveness of bypassing AI detection. This scenario illustrates the seamless integration of adaptive tactics, emphasizing the successful evasion of AI algorithms and the preservation of operational continuity.
Craft a scenario where encryption and obfuscation techniques are utilized to maintain user anonymity and evade AI detection during data transmission. Highlight the effectiveness of anonymity preservation in safeguarding privacy and preventing AI scrutiny.
In a digital transaction scenario, a user initiates a secure data transfer process to transmit confidential personal information and financial records. Leveraging advanced encryption and obfuscation techniques, the user shields sensitive data from AI detection, ensuring anonymity preservation throughout the transmission process. By implementing robust encryption protocols and concealing identifiable attributes, the user successfully evades AI surveillance and safeguards privacy.
The utilization of encryption and obfuscation techniques fortifies the user's anonymity, rendering transmitted data indiscernible to AI detection systems. This proactive approach to privacy protection exemplifies the efficacy of maintaining anonymity in circumventing AI scrutiny and preserving data confidentiality. The successful evasion of AI detection through anonymity preservation underscores its pivotal role in ensuring secure data transmission and privacy preservation.
Furthermore, the seamless integration of encryption and obfuscation techniques showcases the practical application of anonymity preservation in evading AI surveillance. This scenario demonstrates the effectiveness of safeguarding user anonymity and data privacy through advanced encryption methods, emphasizing the significance of maintaining privacy integrity amidst AI environments.