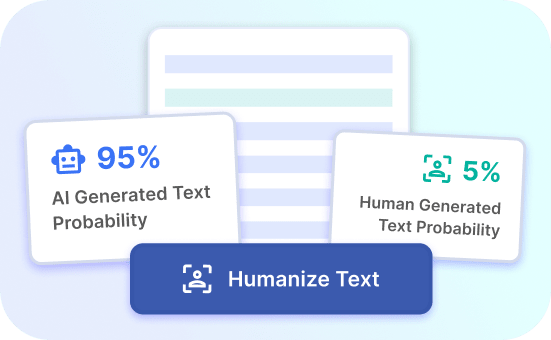
AI Detection Bypassed
Easily bypass AI detection with our advanced solution for seamless operations and enhanced privacy.
AI Bypass Benefits
Enhanced Privacy
Protect your data and operations with our advanced AI detection bypass solution.
Seamless Operations
Keep your processes running smoothly without interruptions from AI detection barriers.
Improved Efficiency
Boost productivity and efficiency by effortlessly bypassing AI detection obstacles.
Bypass AI Detection: Unlocking the Potential of Stealth
Enhanced Privacy Protection
In the digital age, privacy is a growing concern for individuals and businesses alike. By leveraging advanced tactics to bypass AI detection, users can ensure that their online activities remain confidential and inaccessible to unwanted surveillance. With enhanced privacy protection, sensitive information and confidential communications are shielded from prying eyes, offering peace of mind and security in an increasingly interconnected world.
Moreover, bypassing AI detection empowers users to exercise greater control over their digital footprint, minimizing the risk of exposure to potential threats such as identity theft, data breaches, and unauthorized access. This heightened level of privacy protection fosters a secure online environment, allowing individuals and organizations to operate with confidence and assurance.
Try Justdone ->
Unrestricted Access to Content
Bypassing AI detection opens the door to unrestricted access to online content and resources, circumventing geo-blocks and censorship measures that limit the availability of information. Users can seamlessly navigate through digital barriers, ensuring that they can explore a diverse range of content without constraints or limitations. This unrestricted access empowers individuals to leverage the full potential of the internet, accessing educational materials, entertainment options, and valuable resources without geographic boundaries or content restrictions.
Try Justdone ->
Optimized Performance and Efficiency
By bypassing AI detection, users can optimize the performance and efficiency of their digital activities. Without the constraints imposed by detection algorithms, individuals and businesses can streamline their operations, enhance productivity, and minimize disruptions in their online endeavors. This optimized performance enables seamless interactions and transactions, fostering a dynamic and agile digital experience that is free from unnecessary impediments.
Try Justdone ->
Maximizing Your Bypass AI Detection Strategy
Stay Informed with Updates
To stay ahead in bypassing AI detection, it's crucial to stay informed about the latest developments and updates in the field. Keep an eye on emerging trends, technologies, and countermeasures to adapt your strategy effectively. Regularly updating your knowledge base ensures that you can proactively address new challenges and maintain the efficacy of your bypassing methods.
Diversify Your Approach
Diversifying your approach to bypassing AI detection can significantly enhance your success rate. Explore a variety of techniques, tools, and methodologies to create a robust and versatile strategy. By diversifying your approach, you can adapt to evolving detection mechanisms and overcome unique obstacles, establishing a comprehensive and resilient bypassing framework.
Evaluate and Adjust
Continuous evaluation and adjustment are fundamental to the effectiveness of your bypassing strategy. Regularly assess the performance of your tactics, analyze outcomes, and make necessary adjustments to optimize your approach. This iterative process allows you to refine your methods, address vulnerabilities, and adapt to dynamic detection protocols, ensuring the sustained efficacy of your bypassing efforts.
Prioritize Security Measures
While focusing on bypassing AI detection, it's essential to prioritize security measures to safeguard your digital activities. Implement robust security protocols, encryption standards, and privacy-enhancing tools to fortify your online presence. By prioritizing security measures, you can bolster the integrity of your bypassing strategy and mitigate potential risks associated with circumventing detection systems.
Community Engagement and Knowledge Sharing
Engaging with the community and participating in knowledge-sharing initiatives can enrich your understanding of bypassing AI detection. Collaborate with peers, share insights, and contribute to the collective expertise in the field. By fostering a collaborative environment, you can access diverse perspectives, innovative approaches, and valuable resources that enhance the sophistication and effectiveness of your bypassing strategy.
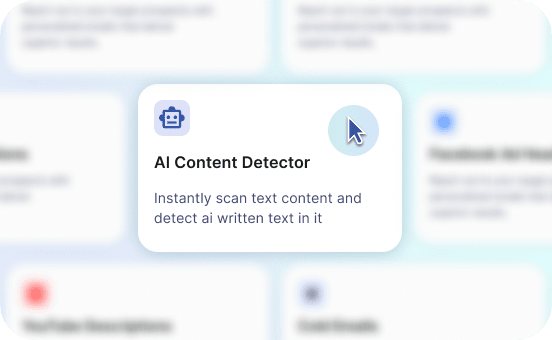
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
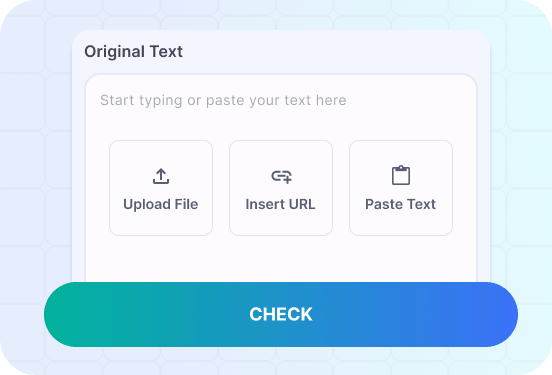
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Unlocking Limitless Potential: Navigating AI Detection Challenges
In the realm of bypassing AI detection, mastering the art of navigating through detection challenges opens doors to limitless possibilities. Embrace the journey of unlocking unrestricted access and unparalleled privacy protection.
Craft a compelling message that showcases the significance of unhindered access to information and the pivotal role of privacy protection in the digital landscape.
In today's interconnected world, accessing information without constraints is paramount to fostering knowledge exchange, innovation, and global connectivity. With the increasing prevalence of online restrictions and surveillance, the ability to bypass AI detection is pivotal in safeguarding privacy and promoting unrestricted access to valuable resources. Embracing advanced bypassing techniques empowers individuals and organizations to transcend digital barriers, ensuring seamless exploration and interaction with diverse content.
Moreover, enhanced privacy protection serves as a cornerstone for maintaining confidentiality, securing sensitive data, and preserving individual autonomy in the digital sphere. By harnessing the capabilities of bypassing AI detection, users can navigate through evolving privacy challenges and establish a resilient shield against intrusive surveillance. The fusion of unhindered access and robust privacy protection forms the bedrock for fostering a dynamic and inclusive digital environment that thrives on open exchange and secure interactions.
As the digital landscape continues to evolve, the need for effective bypassing strategies becomes increasingly pronounced. It is imperative to recognize the indispensable role of privacy protection and unrestricted access in driving innovation, knowledge dissemination, and global connectivity. By embracing the potential of bypassing AI detection, individuals and entities can transcend limitations, amplify their impact, and contribute to a vibrant digital ecosystem that champions freedom and security.
In essence, the ability to bypass AI detection not only unlocks the doors to unrestricted information but also lays the foundation for preserving the fundamental rights of privacy and autonomy in the digital domain. Embracing this capability empowers individuals and organizations to chart new frontiers, foster meaningful connections, and drive positive change in an interconnected world shaped by information and digital interactions.
Craft a response that showcases the seamless integration of privacy protection and unhindered access in the digital realm, emphasizing the transformative potential of bypassing AI detection.
The fusion of privacy protection and unhindered access in the digital realm signifies a transformative shift towards empowering individuals and organizations to navigate through barriers and embrace boundless opportunities. By seamlessly integrating advanced bypassing techniques, users can safeguard their privacy while enjoying unrestricted access to a wealth of information and resources.
In essence, bypassing AI detection serves as a catalyst for transcending limitations, fostering innovation, and fostering a secure digital landscape that thrives on open exchange and uninhibited exploration. This seamless integration not only amplifies the accessibility of information but also upholds the fundamental rights of privacy and autonomy, laying the groundwork for a dynamic and inclusive digital ecosystem.