Unlock AI Detector Limitations
Easily bypass AI content detectors to maximize creative freedom and reach wider audiences without restrictions.
AI Content Freedom
Unrestricted Content Creation
Enjoy the freedom to create without limitations, ensuring your content reaches its full potential.
Enhanced Reach
Bypassing AI content detectors allows you to reach a wider audience and maximize your content's impact.
Boosted Creativity
Liberate your creativity and explore endless possibilities without being confined by AI content restrictions.
Unlocking the Power of Bypass AI Content Detector
Enhanced Content Protection
With the bypass AI content detector, you can safeguard your confidential data and intellectual property by preventing unauthorized access. This advanced tool ensures that only authorized personnel can access sensitive information, adding an extra layer of security to your content.
The AI content detector employs cutting-edge algorithms to detect and block any attempts to bypass security measures. It continuously monitors content access and usage, providing real-time protection against potential threats. By utilizing this tool, you can confidently protect your content from unauthorized distribution and misuse.
Try Justdone ->
Streamlined Workflow Efficiency
By integrating the bypass AI content detector into your workflow, you can streamline content management processes and enhance operational efficiency. This tool automates content monitoring and ensures compliance with security policies, reducing the need for manual oversight.
The AI content detector optimizes content distribution and access, allowing for seamless collaboration while maintaining strict security protocols. With its intelligent features, you can eliminate bottlenecks in content workflows and achieve higher productivity across your organization.
Try Justdone ->
Customizable Security Controls
Empower your organization with customizable security controls using the bypass AI content detector. Tailor security settings to align with specific content requirements and access permissions, ensuring a personalized and adaptive security approach.
This advanced tool enables administrators to define granular access controls, monitor user activities, and implement content usage restrictions. By customizing security controls, you can proactively mitigate risks and uphold compliance standards within your content environment.
Try Justdone ->
Maximizing the Benefits of Bypass AI Content Detector
Regular Security Assessments
Conduct regular security assessments to evaluate the effectiveness of the bypass AI content detector. By periodically reviewing security measures and identifying potential vulnerabilities, you can proactively enhance content protection and reinforce your security posture.
Leverage the insights gained from security assessments to fine-tune security configurations and adapt to evolving threat landscapes. This proactive approach ensures that your content remains resilient against emerging security risks and unauthorized access attempts.
Employee Training and Awareness
Invest in comprehensive employee training programs to increase awareness of the bypass AI content detector and its security features. Educate personnel on best practices for content security, data privacy, and compliance to foster a culture of vigilance and accountability.
Empowering employees with the knowledge to recognize potential security threats and adhere to content security protocols is essential in fortifying overall security resilience. By promoting a security-conscious mindset, your workforce becomes an active line of defense against unauthorized content access.
Continuous Security Updates
Stay updated with the latest security enhancements and feature updates for the bypass AI content detector. Regularly implementing security patches, software updates, and new functionalities ensures that your content security measures remain robust and adaptive to evolving security challenges.
By staying informed about advancements in content security technologies, you can harness new capabilities to fortify your content protection strategies. Embracing continuous security updates empowers your organization to stay ahead of potential security threats and maintain a resilient security posture.
Collaborative Security Governance
Establish collaborative security governance practices to align content security efforts across departments and functional areas. By fostering cross-functional collaboration and communication, you can ensure cohesive security governance that addresses diverse content security requirements and compliance standards.
Encouraging collaboration between security, IT, legal, and content management teams fosters a holistic approach to content security. This collaborative governance model enables comprehensive security oversight and promotes unified security strategies across the organization.
Comprehensive Data Encryption
Implement comprehensive data encryption protocols in conjunction with the bypass AI content detector to safeguard sensitive information. By encrypting data at rest and in transit, you can mitigate the risk of unauthorized access and data breaches, ensuring the confidentiality and integrity of your content.
Leverage robust encryption mechanisms to protect content across various storage and communication channels, bolstering the overall security posture of your organization. Comprehensive data encryption complements the capabilities of the content detector, providing an additional layer of defense for your valuable content assets.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
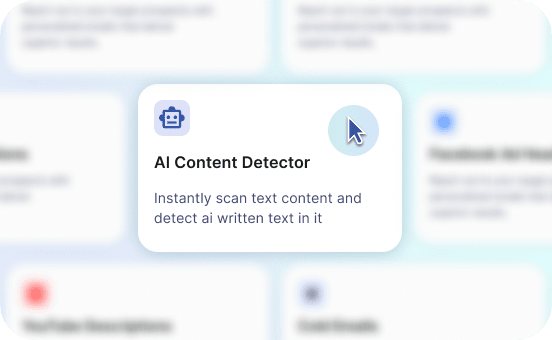
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
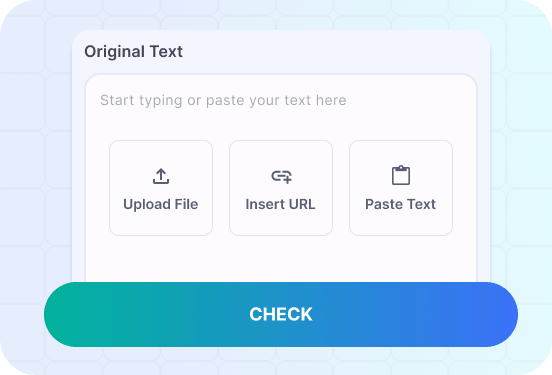
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Empowering Content Security with Bypass AI Content Detector
Explore practical examples of utilizing the bypass AI content detector to reinforce content security and streamline operational workflows.
Craft a compelling narrative that illustrates how the bypass AI content detector effectively controls access to sensitive content, ensuring compliance and data protection.
In a highly regulated industry landscape, ensuring stringent control over content access is paramount to safeguarding sensitive information and upholding compliance standards. The bypass AI content detector serves as a pivotal tool in implementing robust access controls, enabling organizations to define granular permissions and restrictions for content access.
By utilizing this advanced content security solution, organizations can proactively mitigate the risk of unauthorized content distribution and access breaches. The AI content detector empowers administrators to enforce access policies, monitor user interactions, and prevent unauthorized data exfiltration, bolstering overall content security measures.
Furthermore, the AI content detector provides real-time visibility into content access patterns and user behaviors, facilitating proactive threat detection and rapid response to potential security incidents. This comprehensive approach to content access control empowers organizations to maintain data integrity, regulatory compliance, and confidentiality, reinforcing their security posture amidst evolving security challenges.
Leveraging the bypass AI content detector for content access control not only enhances data protection but also streamlines compliance efforts, ensuring that organizations adhere to industry-specific regulations and data privacy mandates. By integrating this advanced tool into content management workflows, organizations can confidently manage content access while upholding the highest standards of security and compliance.
Illustrate a scenario demonstrating the real-time threat monitoring capabilities of the bypass AI content detector, emphasizing its proactive approach to identifying and mitigating potential security risks.
Amidst the evolving threat landscape, organizations require robust mechanisms for real-time threat monitoring to safeguard their valuable content assets. The bypass AI content detector offers unparalleled capabilities in detecting and neutralizing potential security threats through its advanced monitoring and analysis features.
By deploying this innovative content security solution, organizations can proactively identify anomalous content access patterns, unauthorized data sharing attempts, and suspicious user behaviors. The AI content detector leverages machine learning algorithms to continuously analyze content interactions, enabling swift identification of potential security incidents and unauthorized access attempts.
Moreover, the real-time threat monitoring capabilities of the AI content detector empower security teams to respond promptly to emerging threats, preventing potential data breaches and content misuse. This proactive approach to threat monitoring reinforces the overall security resilience of organizations, ensuring that content remains protected against evolving cyber threats and unauthorized access.
With the bypass AI content detector, organizations can embrace a proactive stance towards content security, leveraging real-time threat monitoring to fortify their defenses and maintain the integrity of their valuable content assets in the face of dynamic security challenges.