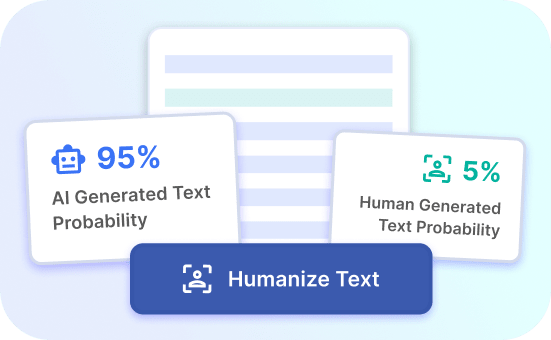
Detect AI Tools Instantly
Identify and analyze AI tools quickly and accurately with our advanced detection technology.
AI Tool Detection Benefits
Instant Recognition
Identify AI tools in a snap, saving time and effort in the detection process.
Accurate Analysis
Ensure precise and reliable analysis of AI tools for enhanced decision-making and insight.
Effortless Detection
Effortlessly detect and categorize AI tools, streamlining workflow and improving productivity.
AI Tool Detection Benefits
Enhanced Security
AI tool detection enhances security by accurately identifying and isolating potential threats. By leveraging advanced algorithms, the tool can swiftly detect any suspicious activity, ensuring the protection of sensitive data and privacy. This proactive approach minimizes the risk of security breaches and unauthorized access.
Moreover, the AI tool detection continuously evolves to recognize new patterns of cyber threats, providing a robust defense mechanism against evolving security challenges. This adaptability ensures that your systems remain safeguarded against the latest cyber threats, granting peace of mind to both businesses and individuals.
Try Justdone ->
Efficient Threat Mitigation
The AI tool detection streamlines threat mitigation processes by swiftly pinpointing and neutralizing potential risks. This rapid identification minimizes the impact of security breaches, ensuring minimal disruption to operations. By automating threat response, the tool enables organizations to efficiently allocate resources to resolve critical security issues, thereby reducing the overall impact on productivity and performance.
Furthermore, the tool's ability to prioritize threats based on severity enables organizations to focus on addressing the most critical vulnerabilities, optimizing their security efforts and resource allocation.
Try Justdone ->
Real-time Monitoring and Analysis
AI tool detection provides real-time monitoring and analysis of network and system activities. This continuous surveillance enables immediate identification of anomalies and potential security breaches, allowing for prompt action to mitigate risks. By analyzing vast amounts of data in real time, the tool ensures that any suspicious activities are promptly detected and addressed, safeguarding the integrity of your systems.
Additionally, the tool's analytical capabilities offer valuable insights into emerging security trends, empowering organizations to proactively enhance their security measures and stay ahead of potential threats.
Try Justdone ->
Effective AI Tool Detection Tips
Regular System Updates
Regularly update your AI tool detection system to ensure that it is equipped with the latest security protocols and threat intelligence. Keeping the system updated strengthens its ability to identify and mitigate emerging cyber threats, enhancing overall security.
Implementing a proactive approach to system updates reduces the risk of vulnerabilities and ensures that your AI tool detection remains effective in safeguarding your digital environment.
Customized Threat Profiles
Tailor the threat profiles within your AI tool detection to align with your organization's specific security needs. By customizing threat profiles, you can focus on detecting threats that are most relevant to your industry, ensuring a targeted and efficient security approach.
Customized threat profiles enable the AI tool detection to prioritize and respond to threats based on their relevance and potential impact, optimizing the overall security posture of your organization.
User Awareness Training
Conduct regular user awareness training to educate employees about the importance of AI tool detection in maintaining a secure digital environment. By fostering a culture of security awareness, employees become proactive contributors to the overall security posture of the organization.
Empowering users with the knowledge to identify and report potential security concerns enhances the effectiveness of AI tool detection by creating an additional layer of vigilance within the organization.
Data Encryption Best Practices
Implement robust data encryption best practices to complement the capabilities of your AI tool detection. Encryption adds an extra layer of security to sensitive data, ensuring that even if a breach occurs, the compromised data remains unreadable and unusable to unauthorized entities.
By integrating data encryption best practices with AI tool detection, organizations can establish a comprehensive security framework that protects data at rest and in transit, safeguarding critical information from potential threats.
Incident Response Simulation
Conduct regular incident response simulations to evaluate the effectiveness of your AI tool detection in identifying and responding to potential security incidents. Simulations enable organizations to assess their readiness to handle security breaches and fine-tune their response procedures.
By simulating various security scenarios, organizations can identify areas for improvement in their incident response processes, enhancing the overall resilience of their security infrastructure.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
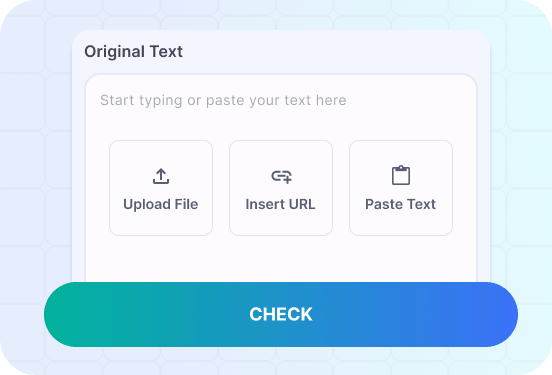
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
AI Tool Detection Examples
Discover the practical application of AI tool detection through the following scenarios, showcasing its capabilities in identifying and addressing security threats in real time.
Create a scenario demonstrating how the AI tool detection identifies and mitigates a network intrusion, highlighting its real-time response capabilities.
In a bustling corporate network, the AI tool detection continuously monitors incoming and outgoing traffic, analyzing patterns and identifying anomalies indicative of a potential intrusion. Suddenly, the system flags an abnormal surge in data requests from an unknown source, signaling a potential threat.
Upon detecting the anomaly, the AI tool detection swiftly isolates the affected network segment, preventing the intrusion from spreading further and minimizing its impact on critical systems. Simultaneously, the tool initiates a real-time analysis of the intrusion, identifying the entry point and potential vulnerabilities exploited by the attacker.
With its advanced threat detection algorithms, the AI tool swiftly neutralizes the intrusion, restoring normal network operations and preventing unauthorized access to sensitive data. The seamless response showcases the tool's real-time monitoring and proactive threat mitigation capabilities, safeguarding the network from potential security breaches.
Illustrate how the AI tool detection identifies and eliminates a malware threat, emphasizing its automated threat response and efficient mitigation.
In a corporate environment, an unsuspecting user inadvertently clicks on a malicious link, unknowingly initiating a malware download. As the malware attempts to infiltrate the system, the AI tool detection immediately recognizes the suspicious behavior, swiftly isolating the affected endpoint to contain the threat.
Utilizing its advanced malware detection algorithms, the tool thoroughly scans the compromised endpoint, swiftly identifying and isolating the malicious code. With its automated threat response capabilities, the AI tool efficiently removes the malware, restoring the integrity of the affected system and preventing the spread of the infection to other network nodes.
The rapid and precise mitigation exemplifies the AI tool detection's ability to autonomously neutralize malware threats, minimizing the impact on organizational operations and preserving the security of digital assets.