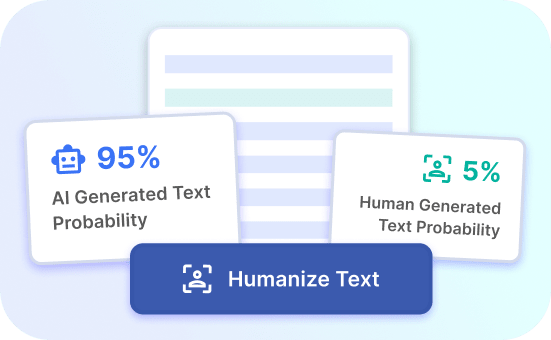
AI Evading Detection
Discover how our AI technology seamlessly bypasses detection, ensuring maximum security and privacy.
Advantages of Our AI
Advanced Stealth Tech
Our AI operates stealthily, evading detection to ensure maximum privacy and security.
Untraceable Intelligence
We provide untraceable technology that bypasses AI detection, keeping your information safe and secure.
Invisible Security
Our AI functions invisibly, evading detection to safeguard your privacy and data.
AI Bypassing AI Detection Benefits
Enhanced Security
AI that bypasses AI detection provides enhanced security by identifying and addressing vulnerabilities in existing systems. By simulating potential threat scenarios, it helps to fortify defenses and prevent unauthorized access. This ensures a robust shield against evolving cyber threats.
Furthermore, this technology allows organizations to stay ahead of cybercriminals by proactively identifying weak points and strengthening security measures. By leveraging AI that bypasses AI detection, businesses can safeguard sensitive data and maintain the integrity of their digital infrastructure.
Try Justdone ->
Improved Threat Detection
AI that bypasses AI detection enhances threat detection capabilities by accurately pinpointing anomalies within networks. Through advanced pattern recognition and behavioral analysis, it can swiftly identify suspicious activities and potential security breaches.
Moreover, this technology empowers organizations to detect sophisticated cyber threats that traditional security measures might overlook. By leveraging AI that bypasses AI detection, businesses can efficiently identify and mitigate potential risks, ensuring comprehensive protection against emerging cyber threats.
Try Justdone ->
Efficient Resource Allocation
AI that bypasses AI detection optimizes resource allocation by prioritizing security measures based on real-time insights. It enables organizations to allocate resources strategically, focusing on areas with the highest vulnerability and potential impact.
Additionally, this technology streamlines security operations by automating threat response and remediation processes. By utilizing AI that bypasses AI detection, businesses can optimize resource allocation, minimize security risks, and maintain operational continuity.
Try Justdone ->
Practical Tips for AI Bypassing AI Detection
Continuous Monitoring
Implement continuous monitoring to proactively detect and mitigate potential security threats. By monitoring network activities in real time, organizations can promptly respond to anomalies and prevent security breaches.
Leverage AI-powered monitoring tools that bypass traditional detection methods, providing comprehensive visibility into network behavior and facilitating early threat detection.
Behavioral Analysis
Utilize AI-driven behavioral analysis to identify abnormal patterns and activities within the network. By analyzing user behavior and network traffic, organizations can uncover potential security risks and unauthorized access attempts.
Implement AI that bypasses AI detection to enhance behavioral analysis capabilities, enabling proactive threat identification and strengthening overall security posture.
Real-time Response
Enable real-time response mechanisms to swiftly address security incidents as they occur. By integrating AI-driven response systems, organizations can automate threat containment and mitigation processes, minimizing the impact of security breaches.
Leverage AI that bypasses AI detection to enable real-time response capabilities, ensuring rapid incident resolution and reducing potential damages to the network.
Adaptive Security Measures
Implement adaptive security measures that evolve in response to emerging threats and attack techniques. By leveraging AI-powered adaptive security solutions, organizations can dynamically adjust their defense mechanisms to counter evolving cyber threats.
Utilize AI that bypasses AI detection to enhance adaptive security measures, ensuring proactive defense against sophisticated and adaptive cyber attacks.
Comprehensive Training
Provide comprehensive training to security personnel on AI-driven detection and response techniques. Equip security teams with the knowledge and skills to effectively leverage AI that bypasses AI detection for proactive threat management.
Invest in specialized training programs to maximize the potential of AI-powered security tools and empower security professionals to effectively safeguard the organization's digital assets.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Exploring AI Bypassing AI Detection
Discover the capabilities of AI that bypasses AI detection through practical examples and applications. Explore how this innovative technology enhances security, threat detection, and proactive defense against evolving cyber threats.
Craft a scenario showcasing the proactive threat detection capabilities of AI that bypasses AI detection in a corporate network environment.
In a bustling corporate network environment, the implementation of AI that bypasses AI detection revolutionizes threat detection and response. As employees access the network from various endpoints, the AI-powered system continuously monitors and analyzes network activities, identifying anomalous behaviors with unparalleled precision.
Through advanced behavioral analysis, the AI system swiftly detects unauthorized access attempts and potential security breaches, empowering the security team to take immediate action. This proactive approach to threat detection ensures that emerging risks are swiftly contained and neutralized, bolstering the overall security posture of the corporate network.
Furthermore, the AI-driven detection capabilities provide comprehensive visibility into network traffic, enabling the identification of subtle anomalies that traditional security measures might overlook. This heightened level of vigilance ensures that potential threats are intercepted before they can inflict harm, fortifying the network's defenses against evolving cyber threats.
With AI that bypasses AI detection, the corporate network operates with heightened resilience and proactive threat management, safeguarding critical assets and maintaining operational continuity amidst the ever-evolving threat landscape.
Illustrate how AI that bypasses AI detection enhances threat detection and response in the e-commerce sector, ensuring robust security for online transactions and customer data.
In the dynamic realm of e-commerce, the integration of AI that bypasses AI detection revolutionizes the security landscape, safeguarding online transactions and customer data with unparalleled efficiency. As e-commerce platforms process a myriad of transactions daily, the AI-powered system continuously monitors and analyzes user behaviors, detecting potential fraudulent activities and security risks in real time.
Through advanced behavioral analysis and pattern recognition, the AI system swiftly identifies anomalies indicative of fraudulent transactions or unauthorized access attempts. This proactive approach empowers e-commerce businesses to preemptively mitigate threats, preserving the integrity of online transactions and ensuring a secure shopping experience for customers.
Moreover, the AI-driven detection capabilities provide adaptive security measures that dynamically adjust to emerging threats, fortifying e-commerce platforms against evolving cyber risks. By leveraging AI that bypasses AI detection, e-commerce businesses uphold robust security standards, inspiring trust and confidence among online shoppers.
With AI that bypasses AI detection, e-commerce security transcends traditional measures, embracing proactive threat detection and adaptive defense mechanisms to uphold the integrity of online transactions and safeguard customer data.