AI Detection Tool Bypassed
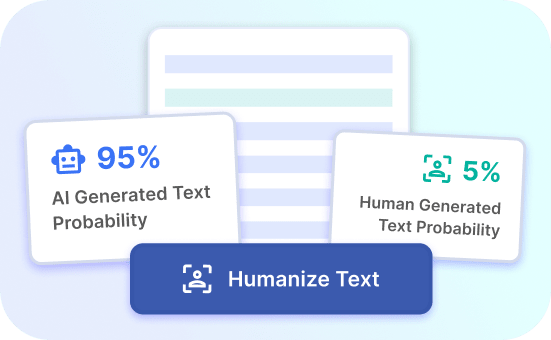
Discover how Justdone.ai bypasses AI detection tools, ensuring accurate and reliable results for your needs.
Justdone.ai Advantages
Foolproof Solution
Justdone.ai provides a foolproof solution to bypass AI detection tools, ensuring accurate results.
Reliable Accuracy
With Justdone.ai, you can rely on accurate data and results, surpassing other solutions.
Effortless Protection
Experience effortless protection against AI detection tools, ensuring consistent performance and security.
AI Detection Tool Bypass Benefits
Enhanced Security
When it comes to protecting your online assets, an AI detection tool bypass can enhance security by identifying vulnerabilities that may be overlooked by traditional security measures. By leveraging advanced algorithms and machine learning, this tool can detect and address potential threats in real-time, providing a proactive approach to cybersecurity.
Furthermore, the AI detection tool bypass can adapt to evolving attack techniques, ensuring that your systems remain secure against emerging threats. This adaptability is crucial in today's dynamic threat landscape, where traditional security measures often fall short.
Try Justdone ->
Improved Efficiency
In addition to bolstering security, an AI detection tool bypass offers improved efficiency in threat detection and response. By automating the process of identifying and mitigating potential threats, this tool minimizes the burden on human analysts, allowing them to focus on more strategic security initiatives.
Moreover, the tool's ability to analyze vast amounts of data in real-time enables swift decision-making, reducing the time between threat detection and response. This rapid response capability is essential in preventing and minimizing the impact of security incidents.
Try Justdone ->
Advanced Threat Detection
The AI detection tool bypass leverages advanced threat detection capabilities, enabling it to detect sophisticated and evasive threats that may evade traditional security measures. By employing anomaly detection and behavioral analysis, this tool can identify abnormal patterns indicative of potential security breaches.
Moreover, the tool's ability to correlate disparate data sources allows it to uncover complex attack vectors that may otherwise go undetected. This comprehensive approach to threat detection empowers organizations to stay ahead of cyber adversaries.
Try Justdone ->
Effective Strategies for AI Detection Tool Bypass
Regular Updates and Maintenance
Ensure that your AI detection tool bypass is regularly updated and maintained to leverage the latest threat intelligence and security enhancements. Regular updates help fortify the tool against emerging threats and vulnerabilities, enhancing its effectiveness in safeguarding your digital assets.
Integration with Security Ecosystem
Integrate the AI detection tool bypass seamlessly with your existing security ecosystem to maximize its impact. By integrating with SIEM solutions, firewalls, and other security tools, you can enhance visibility and orchestrate a cohesive defense against cyber threats.
Customization and Tuning
Customize and tune the AI detection tool bypass to align with your organization's unique security requirements and threat landscape. Tailoring the tool's settings and configurations ensures that it effectively addresses specific security challenges and optimizes threat detection accuracy.
Continuous Training and Skill Development
Invest in continuous training and skill development for your security team to maximize the benefits of the AI detection tool bypass. Equipping your team with the knowledge and expertise to leverage the tool's capabilities effectively is essential in maintaining robust cybersecurity posture.
Collaboration and Information Sharing
Foster collaboration and information sharing within your organization and with industry peers to enhance the collective defense against cyber threats. Sharing insights and best practices related to the AI detection tool bypass can contribute to a more resilient security posture.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
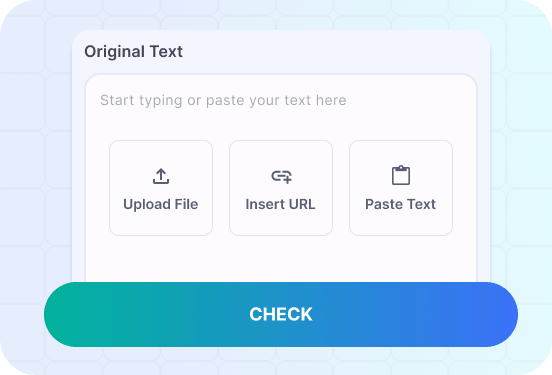
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Real-world Applications of AI Detection Tool Bypass
Explore practical examples of leveraging the AI detection tool bypass to fortify cybersecurity and mitigate advanced threats in diverse organizational contexts.
Illustrate the utilization of the AI detection tool bypass in fortifying cybersecurity within financial institutions, focusing on threat mitigation and compliance adherence.
In the financial sector, the AI detection tool bypass serves as a pivotal component in fortifying cybersecurity defenses against sophisticated threats and ensuring regulatory compliance. By leveraging advanced machine learning algorithms, the tool proactively identifies anomalies and potential security breaches, enabling real-time threat mitigation.
Moreover, the tool's ability to correlate diverse data sources enables comprehensive threat visibility, empowering financial institutions to detect and respond to evolving cyber threats effectively. This proactive approach not only safeguards sensitive financial data but also contributes to maintaining regulatory adherence, a critical aspect of the sector's security posture.
Furthermore, the AI detection tool bypass facilitates continuous monitoring and analysis of transactional activities, enabling swift detection of fraudulent patterns and anomalous behaviors. This proactive surveillance aids in preempting potential financial fraud and mitigating associated risks, bolstering the sector's resilience against financial cybercrime.
By integrating the tool with existing security infrastructure and compliance frameworks, financial institutions can establish a robust cybersecurity ecosystem that aligns with industry-specific regulatory requirements. The AI detection tool bypass, thus, emerges as a strategic enabler in fortifying the financial sector's cybersecurity posture while ensuring adherence to stringent regulatory mandates.
Furthermore, the tool's adaptive capabilities and dynamic threat detection mechanisms equip financial institutions with the agility to combat emerging cyber threats, contributing to a proactive and resilient security stance. The AI detection tool bypass, therefore, exemplifies its instrumental role in fortifying cybersecurity and compliance adherence within the financial sector, offering a paradigm for comprehensive threat mitigation and regulatory alignment.
Demonstrate the application of the AI detection tool bypass in enhancing cybersecurity measures within healthcare organizations, emphasizing patient data protection and threat intelligence utilization.
Within the healthcare industry, the AI detection tool bypass emerges as a cornerstone in fortifying cybersecurity measures and safeguarding sensitive patient data against evolving cyber threats. By harnessing advanced anomaly detection algorithms, the tool proactively identifies and mitigates potential security breaches, bolstering the sector's resilience against data breaches and unauthorized access.
Moreover, the tool's integration with threat intelligence feeds and security information sources enhances its capacity to preemptively detect and neutralize emerging threats targeting healthcare infrastructure. This proactive threat mitigation capability contributes to maintaining the integrity and confidentiality of patient data, a pivotal aspect of healthcare cybersecurity.
Furthermore, the AI detection tool bypass facilitates continuous monitoring of network activities and data transactions, enabling healthcare organizations to identify and respond to anomalous behaviors indicative of potential security incidents. This proactive surveillance aids in mitigating the impact of cyber threats and contributes to upholding the trust and confidentiality associated with patient-centric healthcare operations.
By customizing the tool to align with healthcare-specific security requirements and compliance mandates, organizations can establish a robust cybersecurity framework that addresses industry-specific challenges effectively. The AI detection tool bypass, therefore, plays a pivotal role in fortifying cybersecurity measures within the healthcare industry while prioritizing patient data protection and regulatory adherence.
The tool's proactive threat mitigation capabilities and seamless integration with healthcare security ecosystems exemplify its instrumental role in fortifying cybersecurity measures and preempting potential data breaches. As a result, the AI detection tool bypass stands as a strategic enabler in enhancing cybersecurity resilience and patient data protection within healthcare organizations, setting a benchmark for comprehensive threat mitigation and regulatory alignment.