AI Detection & Prevention
Protect your business from AI-driven threats with advanced detection and prevention solutions.
AI Protection Benefits
Enhanced Security Measures
Benefit from advanced AI-driven security measures that proactively detect and prevent threats, ensuring real-time protection for your business.
Threat Detection Expertise
Leverage cutting-edge AI technology for real-time threat detection, safeguarding your business from evolving AI-driven risks and attacks.
AI-Driven Prevention
Utilize AI-powered solutions to proactively prevent potential threats, ensuring a secure environment for your business operations.
AI Detection and Prevention Benefits
Enhanced Security Measures
AI detection and prevention technology provides enhanced security measures by continuously monitoring and analyzing network traffic, identifying potential threats, and taking proactive measures to prevent security breaches. By leveraging AI, organizations can stay ahead of evolving cyber threats and protect sensitive data from unauthorized access.
Furthermore, AI-powered security solutions can quickly adapt to new attack vectors and patterns, ensuring robust protection against sophisticated cyber threats. This advanced technology significantly reduces the risk of data breaches and strengthens overall cybersecurity posture.
Try Justdone ->
Real-Time Threat Identification
AI detection and prevention systems enable real-time identification of potential security threats by analyzing patterns, behaviors, and anomalies within the network. By leveraging machine learning algorithms, these systems can detect and respond to suspicious activities promptly, minimizing the impact of potential security incidents.
Moreover, the ability to swiftly identify and mitigate threats in real time enhances the overall resilience of the organization's security infrastructure, ensuring continuous protection against emerging cyber threats and vulnerabilities.
Try Justdone ->
Automated Incident Response
AI-driven detection and prevention solutions streamline incident response processes by automating the identification, analysis, and containment of security incidents. This automation not only accelerates the response time to security threats but also reduces the burden on security teams, allowing them to focus on strategic security initiatives.
Additionally, AI-powered incident response capabilities enable organizations to contain and neutralize security threats efficiently, minimizing the potential impact on business operations and mitigating the risk of widespread security breaches.
Try Justdone ->
Effective AI Detection and Prevention Tips
Regular System Updates
Regularly update your AI detection and prevention system to ensure that it is equipped with the latest security patches, threat intelligence, and machine learning models. This proactive approach enhances the system's ability to detect and prevent new and evolving cyber threats, bolstering your overall security posture.
By staying current with system updates, you can effectively mitigate potential vulnerabilities and strengthen your defense against emerging security risks.
Continuous Threat Monitoring
Implement continuous threat monitoring to proactively identify and respond to potential security threats in real time. By leveraging AI-powered monitoring tools, organizations can detect anomalous activities, unauthorized access attempts, and suspicious behaviors, enabling swift and targeted mitigation actions.
Continuous threat monitoring enhances the organization's ability to stay ahead of cyber threats, providing early detection and response to potential security incidents before they escalate.
Employee Training and Awareness
Provide comprehensive training and awareness programs to educate employees about the significance of AI detection and prevention measures. By fostering a security-conscious culture, employees can contribute to the overall security posture by recognizing and reporting potential security threats and adhering to best practices for secure behavior.
Empowering employees with the knowledge and skills to support AI-driven security initiatives strengthens the organization's defense against internal and external security risks.
Data Encryption Practices
Adopt robust data encryption practices to safeguard sensitive information and communications within your network. By encrypting data at rest and in transit, organizations can mitigate the risk of unauthorized access and data breaches, adding an extra layer of protection to critical assets and confidential data.
Effective data encryption practices enhance the confidentiality and integrity of data, reducing the potential impact of security incidents and unauthorized data access.
Collaborative Threat Intelligence Sharing
Engage in collaborative threat intelligence sharing with industry peers and security communities to stay informed about emerging cyber threats and attack trends. By exchanging actionable threat intelligence, organizations can enhance their AI detection and prevention capabilities, leveraging collective knowledge to strengthen their defenses against evolving security risks.
Collaborative threat intelligence sharing fosters a collective security mindset, enabling organizations to proactively adapt to dynamic threat landscapes and bolster their cybersecurity resilience.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
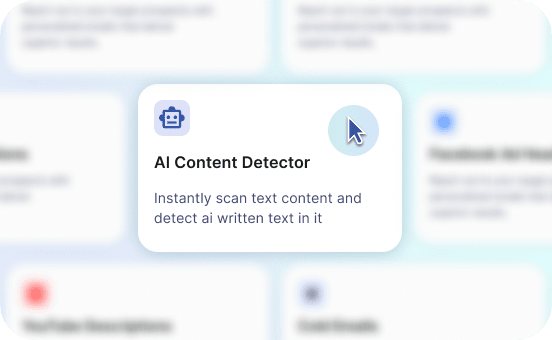
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
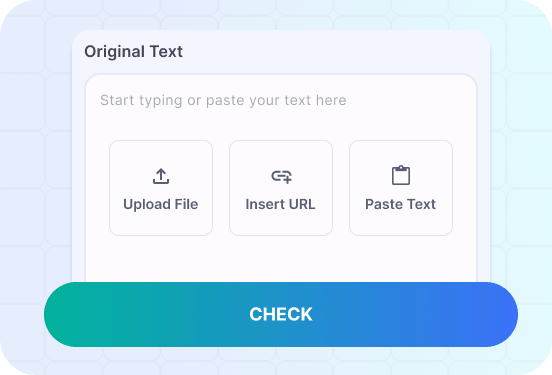
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
AI Detection and Prevention Examples
Explore the practical applications of AI detection and prevention through the following scenarios, showcasing its effectiveness in mitigating security risks and safeguarding critical assets.
Craft a scenario demonstrating the AI system's ability to detect and mitigate a sophisticated phishing attack targeting corporate email accounts.
In a corporate environment, the AI detection and prevention system swiftly identifies a series of suspicious emails containing deceptive links and fraudulent content, indicative of a sophisticated phishing campaign. Leveraging advanced email analysis algorithms, the system detects anomalies in email behavior and content, flagging the malicious messages as potential phishing threats.
Upon detection, the AI system triggers automated email quarantine measures, isolating the suspicious messages and preventing their delivery to employees' inboxes. Simultaneously, the system generates real-time alerts to the security operations team, providing detailed insights into the nature of the phishing attack and the affected email accounts.
Subsequently, the AI system initiates proactive threat response actions, including the automatic removal of malicious emails from the corporate email servers and the implementation of temporary email filters to block similar phishing attempts. Additionally, it conducts behavioral analysis to identify potential email compromise patterns, enabling preemptive measures to secure vulnerable accounts and prevent unauthorized access.
The swift and precise detection and mitigation of the sophisticated phishing attack by the AI system mitigate the risk of employees falling victim to deceptive email schemes, safeguarding sensitive corporate information and preventing potential data breaches. The proactive measures executed by the AI system demonstrate its instrumental role in combating advanced cyber threats, ensuring robust defense against phishing attacks and preserving the integrity of organizational communications.
Illustrate the AI system's capability to identify and respond to insider threats attempting unauthorized access to classified company databases.
In a corporate setting, the AI detection and prevention system detects anomalous user behaviors within the company's database environment, indicating potential insider threat activities. Through advanced user behavior analytics, the system discerns unauthorized access attempts, unusual data retrieval patterns, and atypical database interactions, signaling a potential insider threat scenario.
Upon detection, the AI system initiates automated response actions, such as temporary account suspension and access restriction measures, to prevent further unauthorized activities and data exfiltration attempts. Concurrently, it generates detailed anomaly reports and alerts for the security team, providing comprehensive insights into the identified insider threat behaviors and the affected database assets.
Furthermore, the AI system employs machine learning algorithms to profile normal user behaviors and access patterns, enabling it to distinguish legitimate user actions from suspicious activities. This proactive approach allows the system to adapt its detection capabilities, continuously refining its understanding of insider threat indicators and enhancing its ability to preemptively identify and neutralize potential breaches.
The AI system's swift detection and response to the insider threat activities mitigate the risk of data compromise and unauthorized access to sensitive company databases, reinforcing the organization's defenses against insider threats. By effectively mitigating the potential impact of insider threats, the AI system demonstrates its pivotal role in preserving data confidentiality and thwarting unauthorized internal security risks.