AI Detection Bypass
Discover how Justdone.ai protects your system by outsmarting AI detection, providing advanced security solutions for your business.
Justdone.ai Benefits
Outsmart AI
Stay ahead of AI detection with Justdone.ai's advanced technology, ensuring your system's safety.
Enhanced Security
Experience enhanced security measures that surpass AI detection, providing peace of mind for your business.
Advanced Protection
Benefit from advanced protection against AI detection, safeguarding your business operations effectively.
AI Detection Bypass: Benefits of Using Our Product
Enhanced Security Measures
Our AI detection bypass tool offers enhanced security measures by identifying and addressing vulnerabilities in existing detection systems. By utilizing advanced algorithms and machine learning, our product ensures comprehensive protection against evolving threats and attacks.
With the continuous advancement of AI technologies, traditional detection methods are becoming obsolete. Our solution provides a proactive approach to security, staying ahead of emerging bypass techniques and safeguarding against potential breaches.
Try Justdone ->
Streamlined Operations
Implementing our AI detection bypass tool streamlines security operations by automating the identification and mitigation of bypass attempts. This allows security teams to focus on strategic initiatives and threat response, rather than manually managing routine detection tasks.
By integrating seamlessly with existing security frameworks, our product minimizes operational disruptions while optimizing the overall efficacy of detection protocols. This streamlining of operations leads to improved efficiency and resource allocation within security departments.
Try Justdone ->
Adaptive Threat Response
Our AI detection bypass tool enables adaptive threat response by continuously learning from and adapting to evolving bypass tactics. This dynamic approach ensures that security measures remain effective in the face of sophisticated and rapidly changing threats.
With real-time threat intelligence and adaptive response capabilities, our product empowers organizations to stay resilient against both known and unknown bypass methods, enhancing overall cyber defense strategies.
Try Justdone ->
Effective Strategies for AI Detection Bypass Prevention
Regular System Updates
Regularly updating AI detection systems and algorithms is crucial to staying ahead of potential bypass techniques. By frequently incorporating new threat intelligence and refining detection models, organizations can bolster their defenses against evolving bypass methods.
Behavior-Based Analysis
Implementing behavior-based analysis techniques enhances the accuracy of AI detection systems, enabling the identification of anomalies and potential bypass attempts based on deviations from normal user behavior. This proactive approach strengthens overall threat detection capabilities.
Multi-Layered Authentication
Leveraging multi-layered authentication mechanisms adds an extra barrier against bypass attempts. By combining various authentication factors and continuously verifying user identity, organizations can mitigate the risk of unauthorized access and bypass exploitation.
Anomaly Detection Alerts
Utilizing anomaly detection alerts within AI systems can provide early indications of potential bypass attempts. By configuring real-time alerts for abnormal system behavior, security teams can promptly investigate and mitigate suspected bypass activities.
Continuous Training and Education
Continuous training and education for security personnel on emerging bypass tactics and detection methodologies are essential. Keeping security teams informed and skilled in the latest threat landscapes strengthens the overall resilience of AI detection systems.
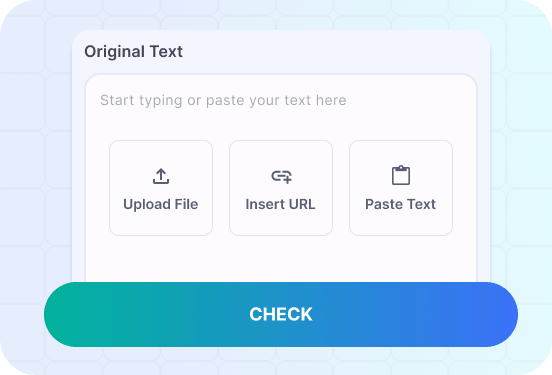
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Real-Life Examples of AI Detection Bypass Scenarios
Explore practical examples of AI detection bypass scenarios and effective countermeasures to enhance your security strategies.
Demonstrate how AI detection bypass tools can identify and mitigate adversarial attacks in real-time scenarios.
In a real-time scenario, our AI detection bypass tool swiftly identifies adversarial attacks through its advanced pattern recognition capabilities. By analyzing deviations from normal user behavior and system interaction, the tool promptly flags suspicious activities for further investigation.
Upon detecting an adversarial attack, the tool triggers automated mitigation protocols, preventing the bypass attempt from compromising system integrity. This immediate response ensures that security measures remain robust and effective in real-time environments, thwarting adversarial bypass tactics effectively.
The AI detection bypass tool's adaptive threat response mechanisms continuously evolve to counter emerging adversarial tactics, providing sustained protection against evolving threats. This proactive approach ensures that organizations can confidently navigate real-time scenarios with heightened resilience against adversarial bypass attempts.
By offering real-time detection and mitigation of adversarial attacks, our AI bypass tool empowers organizations to maintain secure and resilient operational environments. The tool's rapid identification and response capabilities significantly enhance overall security strategies, mitigating the impact of adversarial bypass attempts effectively.
In conclusion, the AI detection bypass tool stands as a formidable defense against adversarial attacks in real-time scenarios, offering proactive identification and mitigation of bypass attempts. Its adaptive response mechanisms and real-time threat intelligence elevate security strategies, safeguarding organizations against evolving adversarial tactics effectively.
With its capability to identify and mitigate adversarial attacks in real-time scenarios, our AI detection bypass tool provides a robust defense against bypass attempts, empowering organizations to navigate dynamic threat landscapes with confidence and resilience.
Illustrate how AI detection bypass tools adapt to emerging adversarial tactics and provide continuous protection against bypass attempts.
In the face of emerging adversarial tactics, our AI detection bypass tool demonstrates its adaptability by swiftly incorporating new threat intelligence and refining detection models to counter evolving bypass methods effectively.
The tool's continuous learning capabilities enable it to dynamically adapt to emerging adversarial tactics, ensuring that security measures remain resilient against evolving threats. By proactively addressing new bypass techniques, the tool offers sustained protection and robust defense mechanisms against adversarial attacks.
Through real-time threat intelligence and adaptive response mechanisms, the AI detection bypass tool maintains a proactive stance against emerging adversarial tactics, safeguarding organizations from the impact of evolving bypass attempts. This adaptability ensures that security strategies remain effective and resilient in the face of dynamic threat landscapes.
By providing continuous protection against bypass attempts, our AI detection bypass tool empowers organizations to navigate evolving adversarial tactics with confidence and resilience. Its adaptive capabilities and proactive defense mechanisms elevate security strategies, mitigating the impact of emerging bypass methods effectively.
In summary, the AI detection bypass tool's adaptability and continuous protection against bypass attempts position it as a crucial asset in countering evolving adversarial tactics. Its proactive stance and dynamic response capabilities enhance the overall resilience of security strategies, safeguarding organizations from the impact of emerging bypass attempts effectively.
Illustrating the tool's adaptability and continuous protection against bypass attempts, our AI detection bypass tool offers a robust defense against evolving adversarial tactics, enabling organizations to navigate dynamic threat landscapes with confidence and resilience.