AI Bypass Detection: Unlocking AI Protection
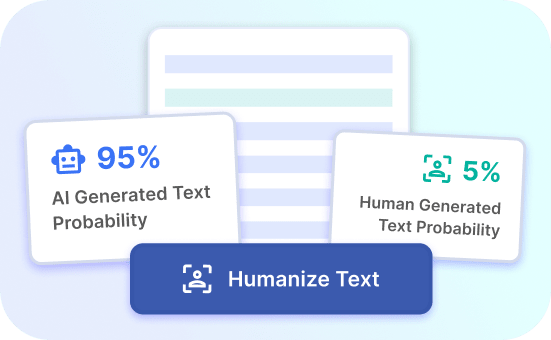
Discover how Justdone.ai's advanced technology outsmarts AI bypass detection and safeguards your systems from sophisticated threats.
Advantages of Justdone.ai
Advanced AI Protection
Justdone.ai offers cutting-edge AI bypass detection to safeguard your systems from advanced threats.
Real-time Security
Benefit from real-time protection and stay ahead of AI bypass techniques with Justdone.ai.
Adaptive Defense
Adapt to evolving AI bypass tactics and ensure seamless protection with Justdone.ai's advanced defense mechanisms.
AI Bypass Detection Benefits
Enhanced Security
AI bypass detection provides enhanced security by preventing unauthorized access to sensitive information. This advanced technology analyzes user behavior and identifies potential threats, ensuring that only authorized users can access the system. By detecting and blocking suspicious activities, it safeguards valuable data and protects against cyber attacks.
Furthermore, AI bypass detection constantly evolves to stay ahead of emerging threats, providing ongoing protection against evolving security risks. This proactive approach helps organizations maintain a secure environment and minimizes the impact of potential security breaches.
Try Justdone ->
Streamlined Operations
Implementing AI bypass detection streamlines operations by automating the identification and mitigation of security risks. This enables organizations to focus on core activities without the burden of manual security monitoring. By leveraging AI technology, businesses can achieve operational efficiency while ensuring robust protection against unauthorized access and data breaches.
Moreover, AI bypass detection reduces the likelihood of false positives, allowing organizations to allocate resources more effectively by addressing genuine security threats. This optimization of operational processes enhances overall productivity and strengthens the security posture of the organization.
Try Justdone ->
Adaptive Threat Response
AI bypass detection offers adaptive threat response capabilities, enabling real-time adjustments to security protocols based on evolving threat landscapes. By dynamically responding to emerging risks, organizations can effectively combat sophisticated cyber threats and prevent potential security vulnerabilities. This adaptive approach ensures that security measures remain effective in the face of evolving attack strategies.
Additionally, AI bypass detection enhances threat visibility by providing comprehensive insights into security events, empowering organizations to proactively address potential vulnerabilities and fortify their defense mechanisms against malicious activities.
Try Justdone ->
Effective Strategies for AI Bypass Detection
Regular System Updates
Regularly update your AI bypass detection system to ensure it is equipped with the latest security patches and enhancements. This proactive measure helps in addressing known vulnerabilities and strengthens the system's resilience against emerging threats. Timely updates are crucial for maintaining robust security defenses and safeguarding sensitive data.
Implementing a systematic update schedule and staying informed about the latest security developments can significantly enhance the effectiveness of AI bypass detection in countering evolving cyber threats.
User Awareness Training
Conduct comprehensive user awareness training to educate employees about the importance of AI bypass detection and the role they play in maintaining a secure environment. By fostering a culture of cybersecurity awareness, organizations can empower their workforce to recognize and report potential security risks, contributing to the overall effectiveness of the AI bypass detection system.
Promoting a security-conscious mindset among employees can serve as a proactive defense against social engineering tactics and help in preventing unauthorized access attempts.
Behavioral Analytics Integration
Integrate behavioral analytics into your AI bypass detection system to enhance its ability to identify anomalous user activities. By leveraging behavioral patterns and machine learning algorithms, organizations can strengthen their security posture and proactively identify potential threats before they escalate. Behavioral analytics integration empowers the AI bypass detection system to adapt to evolving user behaviors and effectively mitigate security risks.
This proactive approach enables organizations to stay ahead of potential security breaches and maintain a robust defense against sophisticated threats.
Incident Response Planning
Develop a comprehensive incident response plan that aligns with the capabilities of AI bypass detection. This strategic approach ensures that the organization is well-prepared to effectively respond to security incidents and mitigate potential impacts. By outlining clear protocols and escalation procedures, businesses can minimize the repercussions of security breaches and swiftly contain any unauthorized access attempts.
Regularly reviewing and updating the incident response plan in alignment with the evolving threat landscape is essential for maintaining the effectiveness of AI bypass detection in mitigating security incidents.
Continuous Performance Evaluation
Conduct regular performance evaluations of the AI bypass detection system to assess its effectiveness in identifying and mitigating security risks. By analyzing system-generated reports and metrics, organizations can gain insights into the system's performance and identify areas for enhancement. Continuous evaluation enables proactive adjustments to security strategies, ensuring that the AI bypass detection system remains resilient in the face of evolving cyber threats.
Utilize the findings from performance evaluations to fine-tune the AI bypass detection system and optimize its capabilities in safeguarding the organization's digital assets.
How to use AI Content Detector
- 1
Choose a template
Select the necessary template from the template gallery.
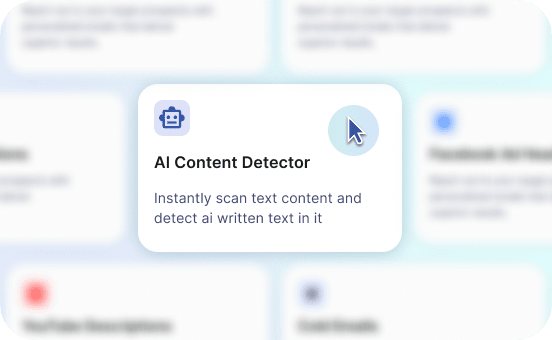
- 2
Provide more details
Fill out the carefully selected inputs to create the best quality of output content.
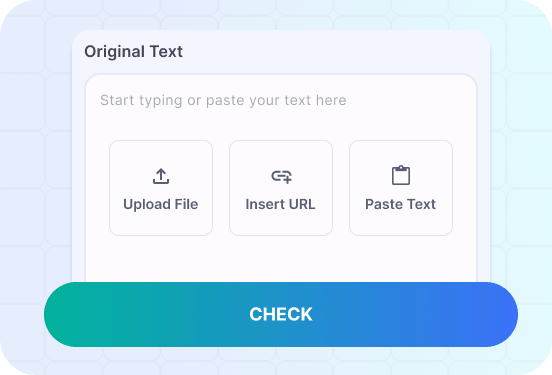
- 3
Enjoy the results
Copy, save for later, rate the output or hit regenerate button.
Real-World Application of AI Bypass Detection
Discover how organizations leverage AI bypass detection to fortify their security measures and proactively mitigate potential threats.
Craft a tailored AI bypass detection solution to bolster security measures for financial institutions and protect sensitive financial data from unauthorized access attempts.
In the financial sector, AI bypass detection plays a pivotal role in safeguarding sensitive financial data and fortifying security measures against potential breaches. By developing a tailored AI bypass detection solution, financial institutions can proactively mitigate potential threats and unauthorized access attempts. Leveraging advanced machine learning algorithms, the system can identify anomalous activities and preemptively block unauthorized access, ensuring the integrity of financial data.
Furthermore, the adaptive threat response capabilities of AI bypass detection enable real-time adjustments to security protocols based on evolving threat landscapes. This dynamic approach empowers financial institutions to effectively combat sophisticated cyber threats and maintain a resilient security posture. By integrating behavioral analytics, the system can proactively identify potential threats before they escalate, enhancing the overall security framework of financial institutions.
The seamless integration of AI bypass detection into the security infrastructure of financial institutions not only safeguards sensitive financial data but also instills confidence among stakeholders regarding the robustness of security measures. This proactive approach to security fortification aligns with regulatory compliance standards and demonstrates the commitment of financial institutions to maintaining a secure environment for sensitive financial information.
Moreover, continuous performance evaluation and regular system updates are essential components of ensuring the effectiveness of AI bypass detection in the financial sector. By conducting thorough performance evaluations and staying updated with the latest security enhancements, financial institutions can optimize the capabilities of AI bypass detection and proactively address emerging security challenges. This strategic approach contributes to the continuous enhancement of security measures and the resilience of financial institutions against evolving cyber threats.
In summary, the real-world application of AI bypass detection in the financial sector highlights its instrumental role in fortifying security measures, protecting sensitive financial data, and proactively mitigating potential threats. By crafting a tailored AI bypass detection solution and integrating advanced security capabilities, financial institutions can uphold a robust defense against unauthorized access attempts and maintain the integrity of financial information.
Implement AI bypass detection to enhance data security in the healthcare industry and safeguard patient information from unauthorized access.
In the healthcare industry, the implementation of AI bypass detection serves as a critical component in enhancing data security and safeguarding patient information from unauthorized access. By leveraging advanced AI technologies, healthcare organizations can strengthen their security posture and proactively mitigate potential threats to patient data. The integration of AI bypass detection enables the identification of anomalous activities and preemptive measures to prevent unauthorized access attempts, ensuring the confidentiality and integrity of patient information.
Additionally, the adaptive threat response capabilities of AI bypass detection empower healthcare organizations to dynamically adjust security protocols in response to evolving threat landscapes. This proactive approach enables healthcare institutions to effectively combat sophisticated cyber threats and maintain a resilient security framework. By integrating behavioral analytics, the system can proactively identify potential threats before they escalate, enhancing the overall security resilience of healthcare organizations.
The seamless integration of AI bypass detection into the healthcare industry's security infrastructure not only enhances data security but also fosters trust among patients and stakeholders regarding the protection of sensitive health information. This proactive approach aligns with regulatory requirements and demonstrates the commitment of healthcare organizations to upholding patient privacy and data security.
Furthermore, continuous performance evaluation and regular system updates are vital for ensuring the effectiveness of AI bypass detection in the healthcare industry. By conducting thorough performance evaluations and staying updated with the latest security enhancements, healthcare organizations can optimize the capabilities of AI bypass detection and proactively address emerging security challenges. This strategic approach contributes to the continuous enhancement of data security and the resilience of healthcare organizations against evolving cyber threats.
In conclusion, the implementation of AI bypass detection in the healthcare industry serves as a proactive measure to enhance data security, safeguard patient information, and mitigate potential threats. By leveraging advanced AI technologies and integrating robust security measures, healthcare organizations can maintain a secure environment for sensitive health data and uphold the trust of patients and stakeholders in the confidentiality of their information.